HTB: Return Walkthrugh
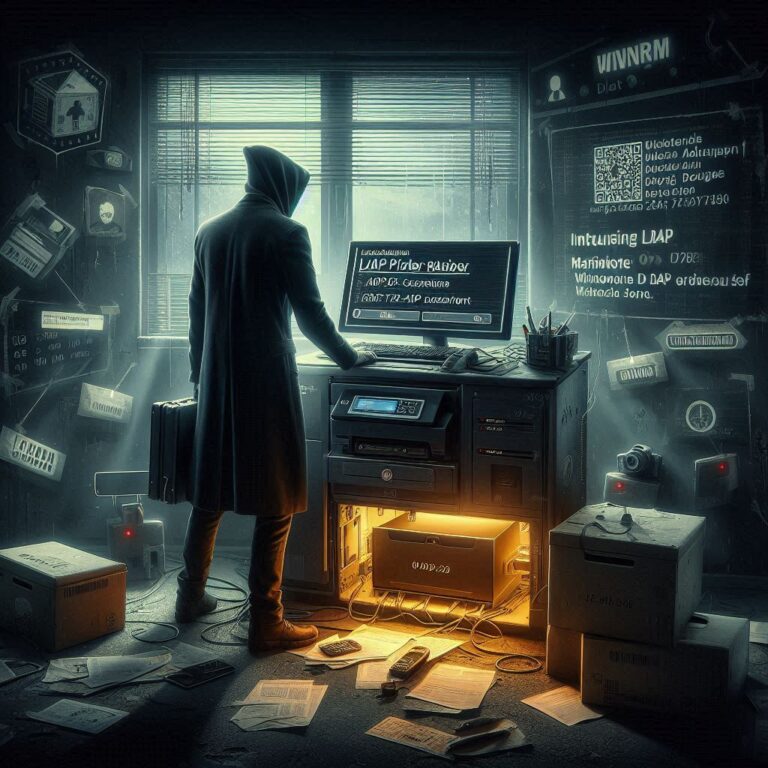
Enumeration NMAP Printer-Page The password field cannot be manipulated to reveal the password. However, the authentication target address can be customized. Set it to your own IP address and listen with netcat on the corresponding port. Exploitation With valid credentials,…